Can Someone Hack My iPhone? 9 Little-Known Loopholes in Security

Your iPhone feels like a fortress, doesn’t it? With Apple’s tight security measures and regular updates, it’s easy to believe your device is impenetrable. But let me tell you something straight up—your iPhone can be hacked.
Shocking, right? And if it happens, it’s not just your data that’s at risk but also your privacy, finances, and peace of mind. So, can someone hack my iPhone? The answer is yes—but the good news is that you can take steps to prevent it.

Let’s break it down in a way that’s simple to understand, practical to apply, and packed with real value.
How Can Someone Hack My iPhone?
Before we dive into solutions, let’s talk about how hackers can target your iPhone. Understanding the risks is half the battle, and believe me, the tactics hackers use can be shockingly simple.

1. Phishing Scams
Imagine this: you get an email or text claiming to be from your bank or Apple, urging you to click a link to "fix an issue." Once you click it, hackers can steal your personal information or install malware on your device.
2. Unsecured Public Wi-Fi
We’ve all been tempted to use free Wi-Fi at coffee shops, airports, or hotels. However, hackers can set up fake networks or intercept data on unsecured connections, gaining access to your private information.
3. Malware-Infected Apps
Have you ever downloaded a free app that seemed too good to be true? Some unverified apps contain malicious software that can infiltrate your iPhone and steal sensitive data.
4. Spyware and Stalkerware
Spyware tools can track your location, monitor your messages, and even listen to your conversations—all without your knowledge. These programs often work silently in the background, making them hard to detect.
5. iCloud Breaches
Your iCloud account holds your photos, documents, and backups. If someone gets hold of your Apple ID credentials, they can wreak havoc by accessing your iCloud data or remotely locking your iPhone.
6. Other Lesser-Known iPhone Hacking Methods & How to Prevent Them
While phishing scams, public Wi-Fi risks, and spyware are commonly known threats, hackers are constantly developing new and sophisticated techniques to infiltrate iPhones. Here are lesser-known hacking methods that could put your data and privacy at risk.
| Hacking Method | How It Works | How to Protect Yourself |
|---|---|---|
| Man-in-the-Middle (MITM) Attacks | Hackers intercept communications between your iPhone and a website, app, or network to steal data. | Use a VPN when browsing, avoid unsecured Wi-Fi, and enable HTTPS-only mode in Safari. |
| Juice Jacking | Malicious charging stations infect your iPhone with malware when plugged in via USB. | Use your own charger, carry a USB data blocker, or charge via a wall adapter instead of public USB ports. |
| Bluetooth Exploits | Hackers can connect to your device via open Bluetooth connections to install malware or steal data. | Turn Bluetooth off when not in use and enable "Allow New Connections" only when necessary in settings. |
| Evil Twin Attacks | Hackers create a fake Wi-Fi network that looks legitimate to trick you into connecting and stealing your data. | Verify network names with staff before connecting and avoid entering sensitive information on public networks. |
How to Tell If Your iPhone Is Hacked?
Are you suspicious that something’s off with your iPhone? Here are some common signs that your device might be compromised:
- Unfamiliar apps: If you see apps you didn’t download, that’s a red flag.
- Battery drains quickly: Hackers could be running apps in the background that drain your battery.
- Strange activity on your accounts: If you notice unfamiliar transactions or messages sent from your accounts, it might be a sign of a hack.
- Overheating: Your phone may overheat if it’s being used to run malicious processes.
- Unexplained data usage: If your data usage suddenly spikes, hackers could be using your phone for unauthorized activities.
- Pop-ups and ads: An increase in pop-up ads or strange behavior from websites could indicate malware on your phone.
If any of these symptoms are present, you’ll want to take immediate action. Here’s how you can fix things.
How to Protect Your iPhone From Hackers

Now that you know how your iPhone can be hacked, let’s focus on solutions. Here are 8 foolproof ways to protect your device and keep hackers at bay:
1. Delete Suspicious Apps
The first thing I want you to do is check your apps thoroughly. Sometimes, hackers install apps on your device that you don't even recognize. These apps can be harmful, gathering your private information or even tracking your activities. If you see any app that you didn’t install or one that just doesn’t seem right, delete it immediately.
To ensure you’re removing all potentially harmful apps:
- Tap and hold the app icon until it begins to wiggle.
- An “X” will appear on the corner of the icon.
- Tap “X” to remove the app from your device completely.
Remember, even if you don’t see any overt signs of malware, it’s still wise to double-check all your installed apps periodically. It’s always better to be safe than sorry.
2. Check for Unrecognized Devices and Remove Them
If someone has hacked your iPhone, there’s a chance that they’ve also gained unauthorized access to your iCloud account. This means other devices—such as a hacker's phone or computer—could be linked to your account and have access to all of your personal information.
You need to check which devices are connected to your iCloud account and remove any unknown ones. To do this:
- For iOS 15 or earlier: Go to Settings > [Your Name] > Devices. You’ll be able to see all devices linked to your iCloud account. If you spot an unfamiliar device, tap on it and select Remove from Account.
- For iOS 16 and later: Use the Safety Check feature. Go to Settings > Privacy & Security > Safety Check. This feature lets you see and manage devices that have access to your data. You can easily remove any suspicious devices here.
This step is crucial in making sure no one else has access to your personal data, contacts, or photos.
3. Update Your Apple ID Password and Enable Two-Factor Authentication (2FA)

One of the first things you should do is change your Apple ID password. If someone gains access to your Apple ID, they can see your private information, make unauthorized purchases, or worse—wreak havoc on your iCloud storage. Here's how you can do this:
- Go to Settings > Sign-In & Security > Change Password.
- Choose a password that’s unique, long (at least 10 characters), and contains a mix of uppercase and lowercase letters, numbers, and symbols.
Once you've updated your password, make sure to enable Two-Factor Authentication (2FA) for extra protection. 2FA adds another layer of security, ensuring that hackers can’t access your account even if they know your password. To turn on 2FA:
- Go to Settings > [Your Name] > Password & Security > Two-Factor Authentication.
- Follow the instructions to set up 2FA. This will require you to verify your identity using another device or your phone number whenever you log in.
4. Report the Hack to Apple
If you think your iPhone has been hacked, it’s a smart move to inform Apple. The company has a dedicated team for investigating security breaches and can help you resolve the situation.
Here’s how you can report the incident:
- Forward suspicious phishing emails to [email protected].
- If there has been fraudulent activity with FaceTime, you can report it to [email protected].
- If you're unable to resolve the issue through email, call Apple Support at 1-800-275-2273 for direct assistance.
Apple may ask for more details about what happened, such as what specific signs made you think your phone was hacked. By reporting the issue, you can gain valuable advice on how to proceed further.
5. Remove Configuration Profiles
A common tactic that hackers use to gain unauthorized access to your iPhone is through configuration profiles. These profiles are sometimes installed by malicious websites or phishing emails. They can provide hackers with control over your device, including your Wi-Fi settings and VPN configurations.
To check for and remove any unwanted profiles:
- Go to Settings > General > VPN & Device Management.
- Look for any configuration profiles that seem suspicious or you didn’t install.
- Tap on the profile and choose Remove Profile.
Removing any unnecessary profiles will help keep your iPhone secure, especially if they’re being used to bypass security settings.
6. Cancel Any Linked Credit Cards
If you’ve noticed suspicious activity on your iPhone, it’s time to take action to prevent financial loss. Hackers could have access to Apple Pay or other payment methods linked to your device. To minimize the impact, immediately cancel any linked credit cards.
Here's what you should do:
- Contact your bank or credit card company and inform them of the unauthorized charges.
- Cancel your card and request a new one.
- Review your bank statements for any fraudulent transactions, and report them to the Federal Trade Commission (FTC) at IdentityTheft.gov.
Canceling your cards will limit the hacker’s ability to make purchases using your financial information. Additionally, be sure to regularly check your account for any unusual activity in the future.
7. Freeze Your Credit
If the hacker has gained access to your personal information, you could be at risk for identity theft. Hackers can use your stolen info to open new accounts in your name or apply for loans. To prevent that from happening, you can freeze your credit at the three major credit bureaus:
- Experian
- Equifax
- TransUnion
By freezing your credit, you prevent anyone from accessing your credit report or opening new accounts in your name. This step is essential in protecting your identity from further attacks.
To freeze your credit, contact each of the bureaus individually. Each one will guide you through the process, and it’s typically free of charge.
8. Factory Reset Your iPhone
After taking all these precautionary steps, if your iPhone still seems to be compromised, a factory reset may be your last resort. A factory reset will wipe your device clean, removing all your personal data, apps, and any malicious software that might be lurking.
Here’s how to reset your iPhone:
- Make sure you back up your data before proceeding. You can back up your data using iCloud or iTunes.
- Go to Settings > General > Transfer or Reset iPhone.
- Tap Erase All Content and Settings.
- Confirm that you want to erase everything. Once completed, your phone will be restored to its original factory settings.

After the reset, you’ll have to set up your device as if it were brand new. While this may seem like a drastic step, it’s often the best way to ensure that all traces of malicious software are completely removed.
Why iPhone Hacking Tools Are Needed
So far, we’ve covered various ways iPhones can be hacked—whether through phishing, spyware, or iCloud breaches. While this is alarming, many people overlook a critical point: hacks don’t always come from strangers.
In many cases, parents worry about their children’s online safety, suspicious behavior, or the risks of cyber threats. Employers may need to ensure company devices are not being misused. Partners in relationships may feel concerned about digital privacy and transparency.
This brings us to a pressing question: Is it possible to hack an iPhone without being detected? That’s where SafeMyKid comes in.
How to Hack an iPhone Using SafeMyKid

SafeMyKid is a must-have tool for iPhone users. It is designed to help parents monitor and protect their kids’ online activities; it has hacking features that make it invaluable for anyone who wants to hack someone's iPhone.
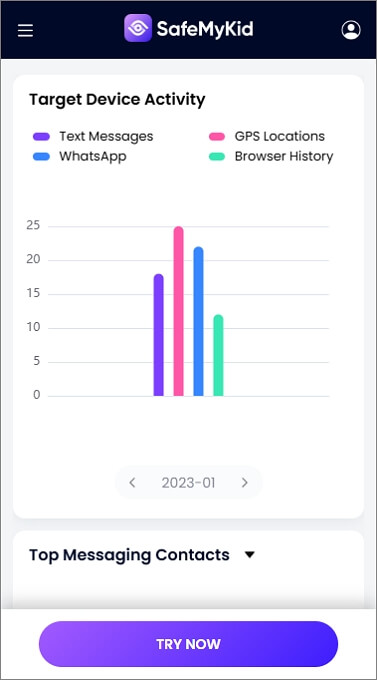
Key Features of SafeMyKid
- Discreet Monitoring: SafeMyKid works silently in the background, so your device’s performance won’t be affected.
- Detailed Usage Reports: The app provides comprehensive reports about browsing history, app usage, and more.
- Website Blocking: Want to block harmful or suspicious websites? SafeMyKid lets you do that with ease.
- Cross-Device Compatibility: Monitor multiple devices from a single dashboard.
- Real-Time Alerts: Get instant notifications about any unusual activity on your device.
How SafeMyKid Can Help You Hack Someone’s iPhone
Setting up SafeMyKid is quick and hassle-free. Follow these simple steps:
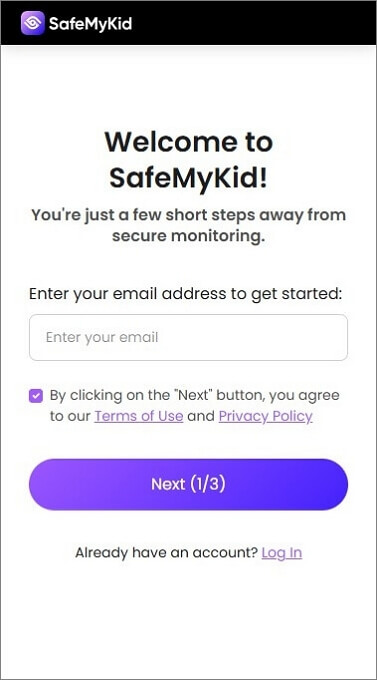
Step 1.Create an Account
Visit the SafeMyKid website and sign up using your email address. Choose a subscription plan that suits your needs.
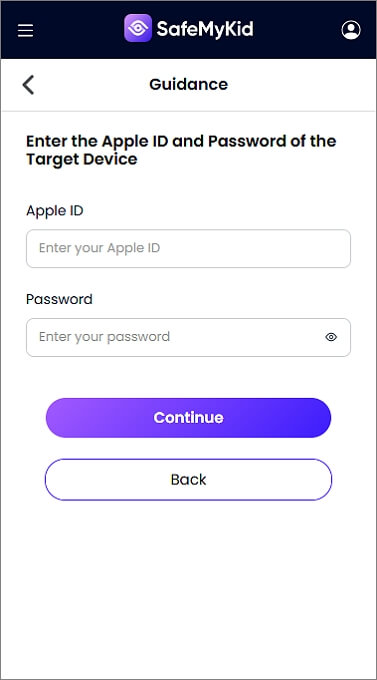
Step 2.Set Up SafeMyKid
For iPhones, there’s no need to install an app. Simply log in with your iCloud credentials to activate monitoring. Don’t worry—SafeMyKid doesn’t store your iCloud password. It uses secure encryption to protect your data.
Step 3.Customize Settings to Hack an iPhone
Use SafeMyKid to hack the target iPhone. With this, you can block specific websites, track browsing history, and monitor app usage. You can also set up alerts for specific activities or websites.
Why Choose SafeMyKid?
SafeMyKid isn’t just another app; it’s a comprehensive security solution. Here’s why it stands out:
- Ease of Use: Even if you’re not tech-savvy, you’ll find the interface intuitive and user-friendly.
- Complete Privacy: Your data is secure, and SafeMyKid ensures discreet monitoring without compromising trust.
- Versatility: Whether you’re a parent or an individual user, SafeMyKid adapts to your security needs.
FAQs about iPhone Hacking and Security
To wrap up this comprehensive guide, here are some of the most frequently asked questions about iPhone hacking and security. These answers will help you understand the risks, recognize potential threats, and take the right steps to protect your device and data.
1. Can hackers make purchases on my iPhone?
Yes, if your iPhone is hacked, the hacker may have access to your Apple Pay or credit card information. Immediately cancel any linked payment methods and report fraudulent transactions to your bank and Apple. It’s also a good idea to freeze your credit to prevent further misuse of your financial information.
2. What is the Safety Check feature, and how can it help me?
The Safety Check feature in iOS 16 and later allows you to review and manage who has access to your personal information and devices. This tool helps you quickly remove any unrecognized devices or people who may have unauthorized access to your iPhone, iCloud, or personal data.
3. Should I freeze my credit if my iPhone is hacked?
Yes, freezing your credit is a smart move if your iPhone has been hacked and you believe your personal information may have been compromised. Freezing your credit prevents anyone from accessing your credit report or opening new accounts in your name, providing an extra layer of protection against identity theft.
4. Is it safe to use public Wi-Fi with my iPhone?
Public Wi-Fi networks are not always secure, making it easier for hackers to access your device. When using public Wi-Fi, consider using a VPN (Virtual Private Network) to encrypt your connection and protect your data. Avoid logging into sensitive accounts or making purchases while connected to public Wi-Fi.
Final Thoughts
So, can someone hack my iPhone? The answer is yes. With SafeMyKid, you can discreetly monitor activity, track messages, and even view social media interactions—all in real time.
Whether you're testing vulnerabilities or just curious about iPhone security loopholes, this tool makes it effortless. Discover step-by-step how to leverage apps to bypass restrictions and access data undetected.


