Number to Dial to See If Your Phone Is Tapped: 9 Ways to Check

Do you ever feel like someone might be listening to your calls or tracking your phone without your knowledge? With the rise of digital surveillance and hacking, phone tapping has become a growing concern. If you suspect that your phone is being monitored, there are ways to check for unauthorized access.
Certain dial codes can reveal whether your calls or messages are being forwarded, if hidden spyware is installed, or if unusual activity is occurring on your device. In this guide, we’ll walk you through the essential numbers to dial to see if your phone is tapped and explain how to protect your privacy.

Signs Your Phone Might Be Tapped
If your phone is being tapped, there are often subtle but noticeable signs that something isn’t right. From performance issues to strange noises during calls, these red flags can indicate unauthorized surveillance or spyware activity on your device.
Unusual Battery Drain: If your phone battery drains faster than usual, spyware may be running in the background, constantly transmitting your data.

Excessive Data Usage: Spyware often sends stolen information over the internet, which can cause a sudden spike in mobile data consumption.

Strange Background Noise During Calls: If you hear static, clicking, or beeping sounds during conversations, it could indicate phone tapping.
Delays in Shutting Down or Unusual Behavior: A tapped phone may take longer to power off because spyware is running in the background.

If you notice these issues, use the dial codes below to investigate further.
Dial Codes to Check If Your Phone Is Tapped
If you suspect that someone may be monitoring your calls or messages, using specific dial codes can help you detect unauthorized redirections or call forwarding. These codes provide a quick and easy way to check if your phone is compromised and take necessary action to secure your device.
1. Dial #21# – Check Call Forwarding Status
What It Does: This code shows whether your calls, messages, or data are being forwarded.
How to Use:
- Open your dial pad and enter #21#, then press Call.
- A message will appear showing if your calls are being forwarded.
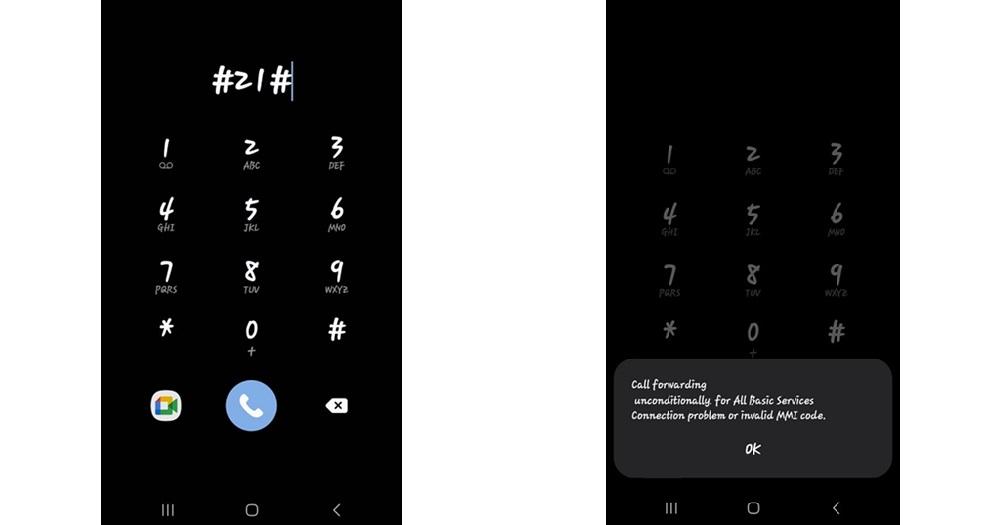
Why It Matters: If your calls are being redirected to an unknown number, your phone may be tapped.
2. Dial #62# – Find Out Where Calls Are Being Forwarded
What It Does: This code reveals the number your calls are redirected to when your phone is unreachable.
How to Use:
- Dial ** #62#* and press Call.
- The screen will display any number receiving your calls.
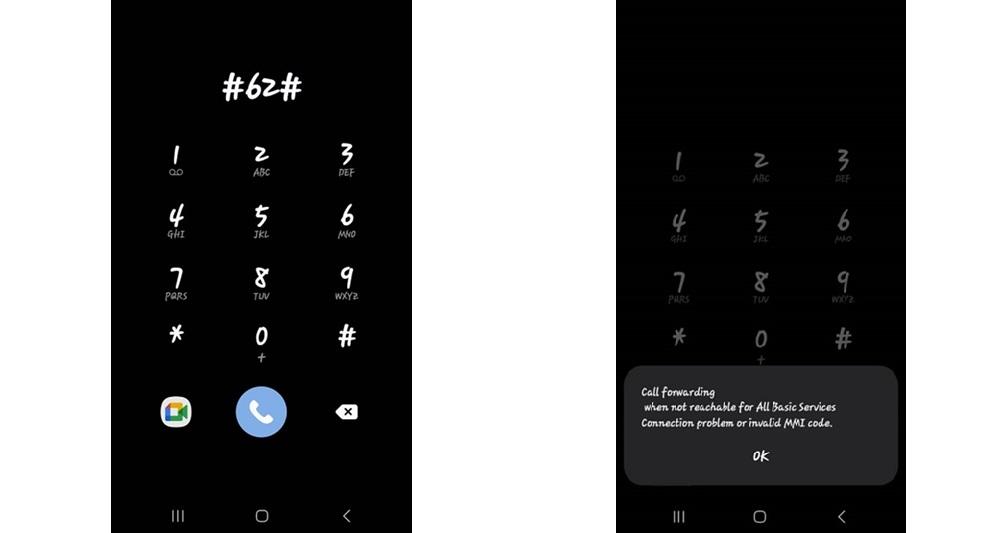
Warning: If you see an unknown number, your phone may be compromised.
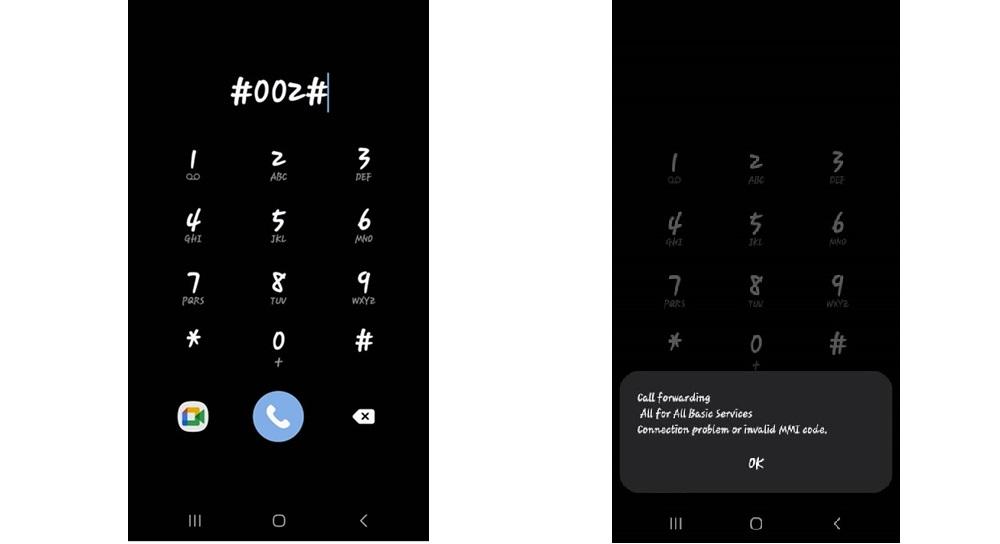
3. Dial ##002# – Disable Call Forwarding
What It Does: This code turns off all call forwarding on your device.
How to Use:
- Dial ##002# and press Call.
- Your screen will confirm that call forwarding has been disabled.
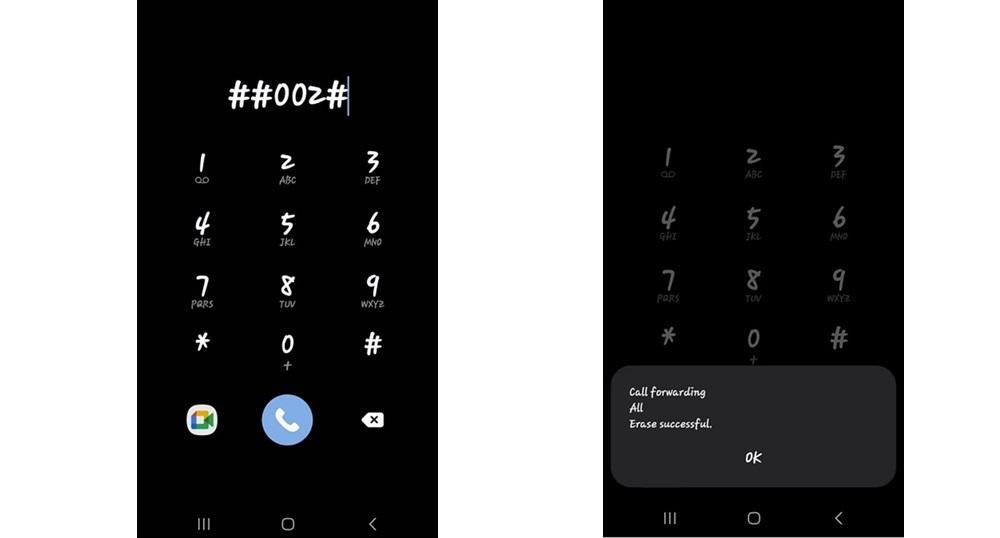
Tip: This is a great way to block potential tracking attempts.
4. Dial* #06# – Check Your IMEI Number
What It Does: This code reveals your phone’s unique IMEI number, which can help identify cloning or tracking.
How to Use:
- Dial *#06# and press Call.
- Your IMEI number will be displayed on the screen.
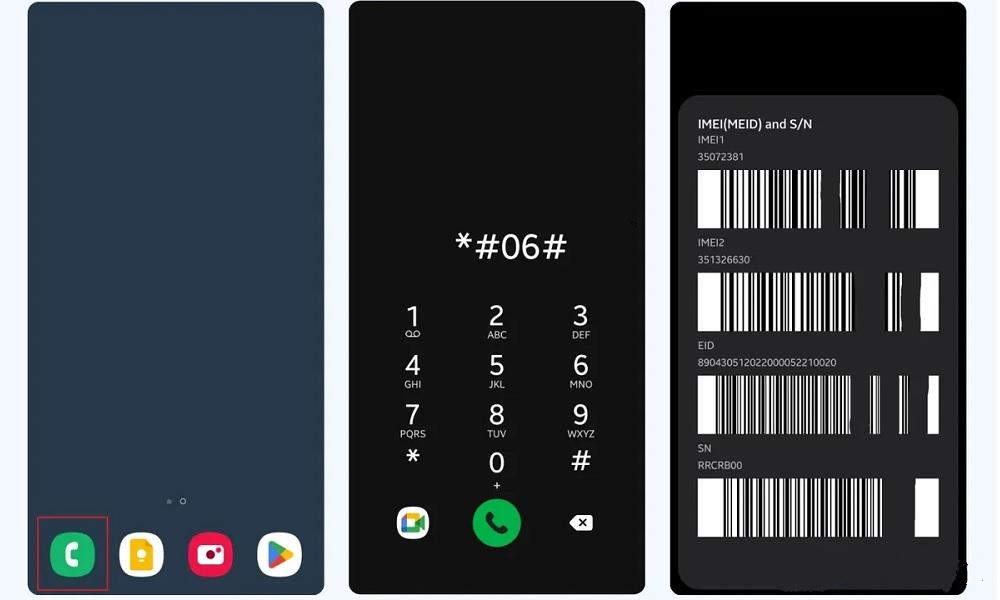
Why It Matters: If your IMEI number is altered or used on another device, your phone may have been cloned.
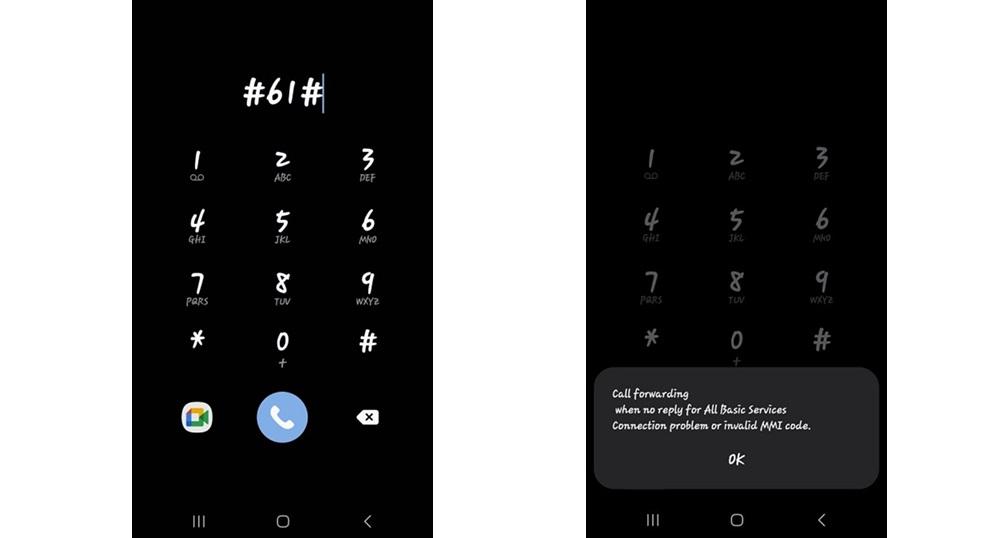
5. Dial #61# – Check Missed Call Forwarding
What It Does: Shows if your calls are being forwarded when you don’t answer.
How to Use:
- Dial ** #61#* and press Call.
- The screen will display any forwarded numbers.
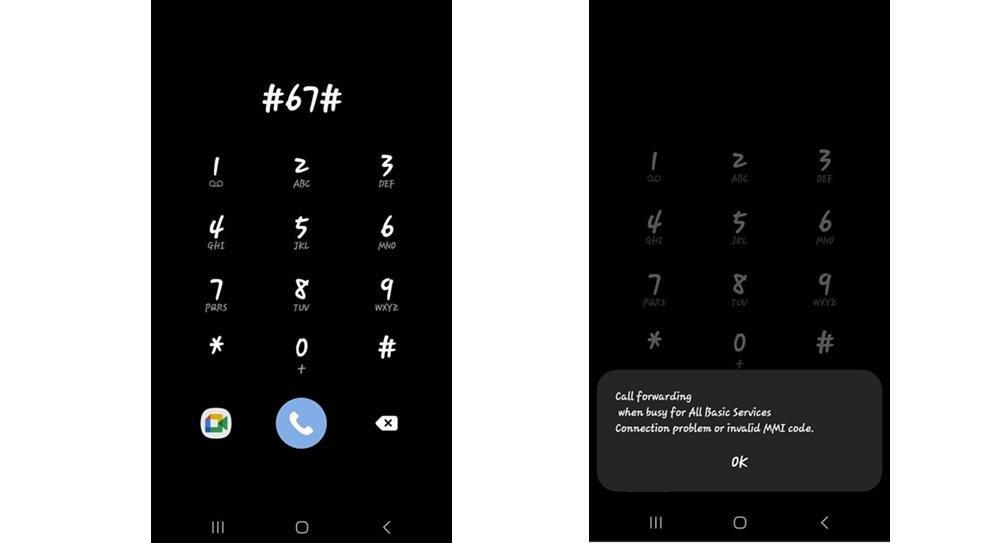
6. Dial #67# – Check When You’re on Another Call
What It Does: Find out if your calls are being forwarded when your line is busy.
How to Use:
- Dial #67# and press Call.
- The screen will display if your calls are being redirected.
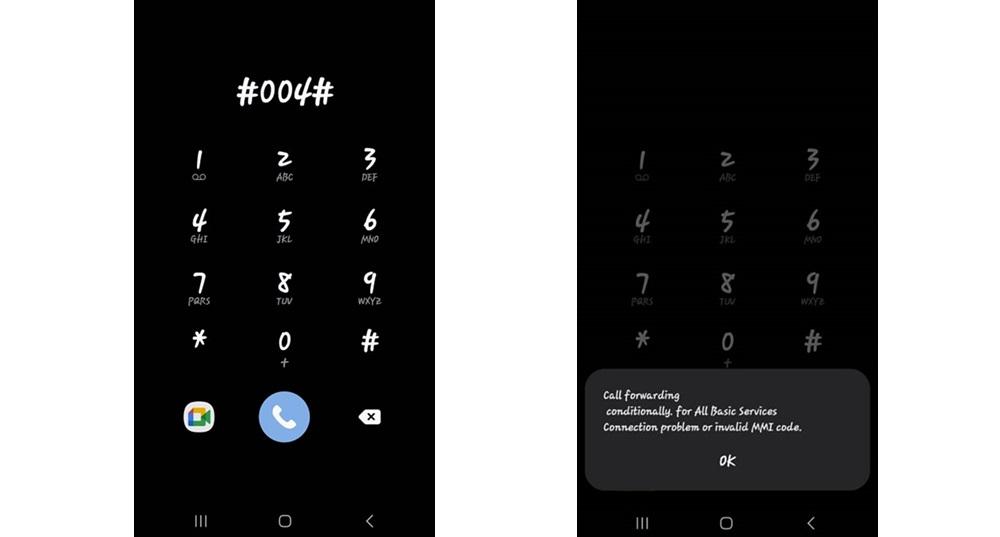
7. Dial #004# – Check Conditional Call Forwarding
What It Does: Displays all conditional call forwarding settings.
How to Use:
- Dial ** #004#* and press Call.
- Check if unknown numbers appear in the results.
8. Dial #002# – Reset All Forwarding Settings
What It Does: Cancels all call forwarding, ensuring your phone isn’t secretly redirecting calls.
How to Use:
- Dial #002# and press Call.
- Check if all call forwarding settings have been reset.
9. Dial #43# – Check Call Waiting Status
What It Does: Reveals if call waiting is enabled.
How to Use:
- Dial #43# and press Call.
- Check your call waiting status

SafeMyKid – The Best Solution for Tracking & Protection
Ensuring your privacy is protected is more important than ever these days. While official code dialing can help identify potential threats, they don’t offer real-time protection or detailed insights into unauthorized activity on your phone. This is where SafeMyKid stands out as the best solution.
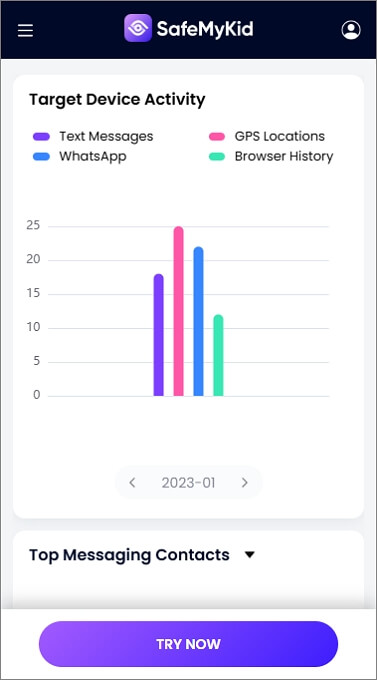
SafeMyKid is not just another phone monitoring tool—it is a comprehensive mobile security solution that allows you to track, detect, and eliminate spying activities before they compromise your personal data. Designed with advanced security algorithms, SafeMyKid actively monitors your device for suspicious activity, offering real-time alerts, detailed reports, and complete control over your phone’s security.
![]()
Key Features of SafeMyKid for Tapping a Phone
SafeMyKid is designed as an all-in-one monitoring tool, allowing users to track and monitor a target phone discreetly. Below are some of its standout features:
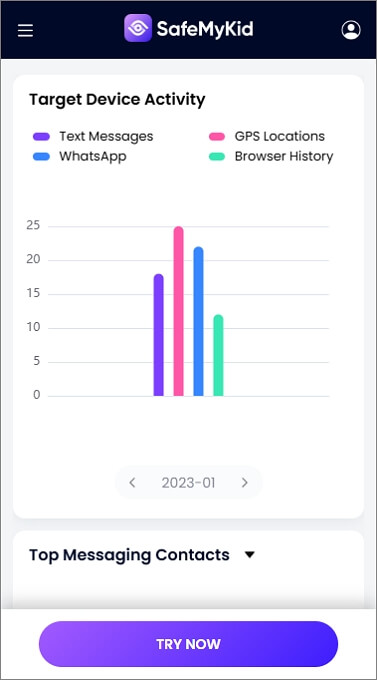
- Live Call and SMS Monitoring – SafeMyKid enables real-time tracking of calls and messages on the target device, helping users see who their target is communicating with.
- Advanced GPS Location Tracking – With real-time location tracking, SafeMyKid allows users to monitor a phone’s movements and set geofencing alerts to track specific locations.
- Spyware and Hidden Apps Detection – While SafeMyKid is primarily used for monitoring, it can also detect and remove spyware on the target device, preventing third-party apps from interfering with tracking.
- Network and Wi-Fi Tracking – The app provides insight into the networks the target phone connects to, allowing users to see if the device is accessing unknown or suspicious networks.
- Stealth Mode Monitoring – SafeMyKid runs in the background without alerting the target user, ensuring discreet tracking of calls, messages, and locations.
With these features, SafeMyKid offers a comprehensive way to monitor a phone’s activity without being detected, making it a powerful tool for those looking to keep an eye on someone’s mobile interactions.
How to Use SafeMyKid for Phone Tapping
SafeMyKid enables you to discreetly track a phone’s activities, monitor calls and messages, and detect hidden apps that may indicate surveillance. Here’s how you can use it for effective phone monitoring.
How to Perform an Android Phone Tapping
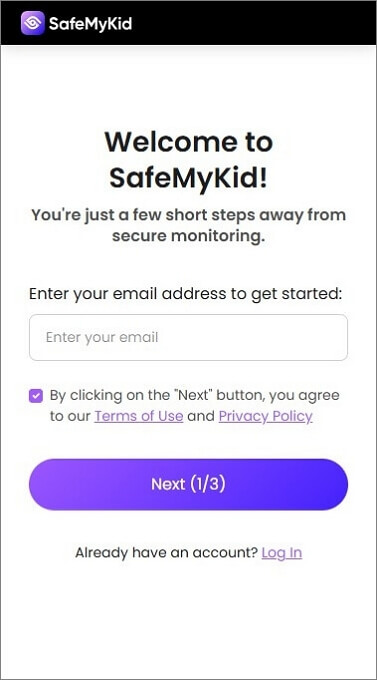
Step 1. Sign up
Create your account using a valid email address.
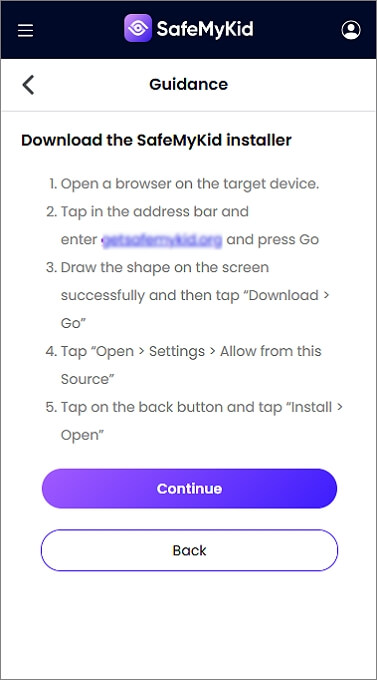
Step 2. Set Up the SafeMyKid App
Install the app directly on the phone that you want to tap. Follow the easy on-screen instructions.
Step 3. Tapping with SafeMyKid
Log in to your SafeMyKid dashboard to monitor activities and view alerts on the tapped device in real time through SafeMyKid’s online dashboard.
How to Perform an iPhone Tapping
Step 1. Sign Up
Create your free account by entering your valid email address.
Step 2. Configure SafeMyKid
Do not install the app! Simply set up SafeMyKid on your target device using only the owner’s iCloud details.
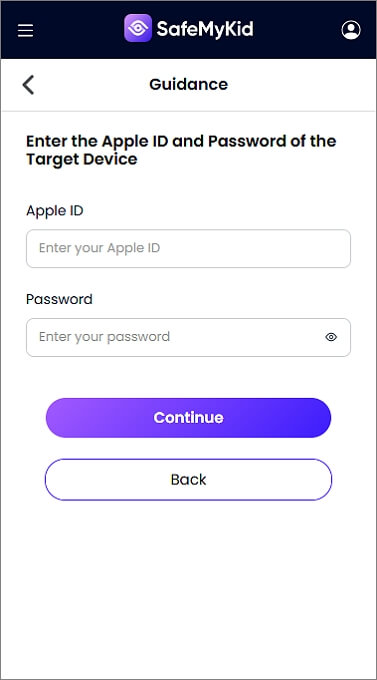
Step 3. Monitor the Tapped Device Using SafeMyKid
Begin to use SafeMyKid to monitor activities and receive alerts from the online dashboard.
Why SafeMyKid is The Most Reliable Tool for Phone Tapping
SafeMyKid offers a seamless and non-intrusive way to monitor a phone’s activities. It provides real-time alerts on suspicious behaviors, detects hidden spyware or monitoring apps, and helps track unusual call forwarding or data usage patterns. Whether you're concerned about privacy breaches, tracking attempts, or unauthorized surveillance, SafeMyKid is a powerful and user-friendly solution for monitoring mobile activity discreetly.
Official vs. Third-Party Methods for Checking Phone Tapping
There are multiple ways to check if your phone is tapped, ranging from official carrier-supported methods to third-party security apps. Understanding the advantages and limitations of each can help you choose the best approach to safeguard your privacy.
Official Methods (Pros & Cons)
- Carrier Support: Network providers can run diagnostics to detect phone tapping.
- Built-in Phone Settings: Use official system codes to reset unauthorized call forwarding.
- Limited Detection: Official methods cannot always detect advanced spyware.
Limitations of Third-Party Apps
- Some security apps may require rooting or jailbreaking, which can compromise device security.
- Not all third-party apps provide real-time monitoring like SafeMyKid does.
How to Protect Your Phone from Tapping
With the rise of spyware and surveillance tools, protecting your phone from unauthorized tapping is crucial. Hackers, cybercriminals, and even unethical organizations can exploit vulnerabilities in your device to listen to your calls, read messages, and track your location. Here are essential steps to safeguard your privacy:
1. Check and Disable Call Forwarding
Some spyware reroutes your calls to another number without your knowledge. To disable all call forwarding, dial:
##002# and press Call.
This resets all conditional call forwarding settings and ensures your calls stay private.
2. Scan for Spyware with Security Apps
Use trusted security apps like SafeMyKid, Norton Mobile Security, or Malwarebytes to detect and remove spyware that may be secretly running on your device. These apps can scan for suspicious software, alert you to security risks, and provide real-time protection.
3. Keep Your Software Up to Date
Regularly updating your operating system (iOS or Android) and installed apps ensures that security patches fix known vulnerabilities. Spyware often exploits outdated software, so enabling automatic updates is recommended.
4. Avoid Public Wi-Fi and Use a VPN
Public Wi-Fi networks are hotspots for cyberattacks, making it easier for hackers to intercept your data. If you must use public Wi-Fi, use a Virtual Private Network (VPN) like NordVPN, ExpressVPN, or ProtonVPN to encrypt your internet connection and protect your information.
5. Monitor Battery and Data Usage
A sudden increase in battery drain or unexpected spikes in data usage can indicate the presence of spyware. Check your phone's settings to see which apps are consuming excessive power and data, and remove any suspicious ones.
6. Use Strong Authentication and Encryption
- Enable Two-Factor Authentication (2FA) for added security.
- Use a strong, unique password for your phone and apps.
- Turn on device encryption to protect your stored data from unauthorized access.
7. Factory Reset if Necessary
If you strongly suspect your phone is compromised and cannot remove spyware, perform a factory reset to erase all data and reinstall the operating system before doing so, back up important files to a secure location.
What to Do If Your Phone Is Tapped
If you suspect that your phone is being monitored, taking immediate action is essential to protect your privacy. Here are a few steps you can take to detect and remove potential threats:
- Remove Suspicious Apps: Uninstall any apps that you don’t recognize from your phone settings.
- Perform a Factory Reset: Resetting your phone to factory settings eliminates spyware and hidden tracking apps.
- Contact Your Carrier: Report any unusual activity to your service provider. They can help disable unauthorized redirections.
Frequently Asked Questions (FAQs) on Numbers to Dial to See if Your Phone is Tapped
If you suspect that your phone is being monitored, dialing certain codes can help reveal signs of unauthorized access. Below are some common questions and answers to help you understand how phone tapping works and what you can do about it.
1. Can someone tap my phone without me knowing?
Yes, hackers, government agencies, or even malicious individuals can tap your phone without your knowledge. They might use spyware, exploit vulnerabilities, or gain unauthorized access to your call-forwarding settings. Monitoring for unusual activity is key to staying secure.
2. If I reset my phone, will it remove phone tapping?
A factory reset removes most spyware and hidden tracking apps. However, if the spy software was installed at a deeper system level (e.g., firmware modifications or remote network monitoring), additional security measures like SafeMyKid are recommended for detection and prevention.
3. Can my phone be tapped if I only use Wi-Fi?
Yes, even if you don’t use cellular data, hackers can intercept your information through compromised or fake Wi-Fi networks. Using SafeMyKid's Wi-Fi protection feature can help detect unsecured connections that could be used for spying.
4. Is it legal for someone to tap my phone?
In most countries, wiretapping without consent is illegal. However, law enforcement agencies can obtain permission to tap a phone under certain circumstances. Employers, partners, or hackers using spy apps without consent are usually breaking the law.
5. Can Bluetooth connections be used to tap a phone?
Yes, Bluetooth vulnerabilities can allow attackers to remotely access your phone, extract data, or install spyware. Always turn off Bluetooth when not in use, and avoid pairing with unknown devices.
6. Do call recording apps mean my phone is tapped?
Not necessarily. Many legitimate apps record calls for personal or business purposes. However, if you notice unknown call recordings in your system files, or your phone records conversations without permission, this could indicate hidden spyware.
7. Can someone hack my phone just by calling me?
No. A simple phone call does not install spyware on your device. However, some scam calls trick users into downloading malicious apps or revealing personal information, which can lead to unauthorized access.
Conclusion
Understanding the numbers to dial to see if your phone is tapped is a crucial step in identifying potential security threats. While these codes can help detect unauthorized access, they may not always provide a complete picture.
For a more comprehensive approach to safeguarding your privacy, SafeMyKid offers real-time monitoring and advanced security features. Stay proactive, protect your data, and ensure your device remains secure.


