How to Hack Instagram Account: Top 5 Methods Revealed

There are situations where you might want to know how to hack Instagram account –you might want to recover lost credentials, monitor a child’s online activity for safety reasons, or check a partner’s interactions.
In this article, we will explore five methods that have been commonly used to hack Instagram accounts, breaking down how each works and their limitations.

Why Someone Might Want to Hack an Instagram Account
Hacking an Instagram account can be driven by various motivations—some ethical and legal, while others fall into gray or illegal territory. Below are some of the most common reasons why individuals may seek access to an Instagram account:

- Parental Monitoring for Child Safety
- Recovering a Lost or Hacked Account
- Investigating Cyberbullying or Harassment
- Employee Monitoring on Company-Owned Devices
- Ethical Hacking and Security Testing
- Relationship and Trust Issues
Parents often worry about their children’s online activities, especially on social media platforms like Instagram. With cyberbullying, inappropriate content, and online predators becoming more prevalent, parents may use monitoring tools to ensure their children’s safety by tracking messages, posts, and interactions.
Many people lose access to their Instagram accounts due to hacking attempts, forgotten passwords, or accidental logouts. In such cases, ethical hacking techniques, such as retrieving data through linked emails or security questions, can help users regain control of their accounts.
Victims of cyberbullying or online harassment may want to access an account to gather evidence against an attacker. This is especially common among parents, law enforcement officials, or organizations investigating digital crimes.
Some businesses monitor their employees’ social media activity on company-owned devices to prevent data leaks, maintain professionalism, or ensure compliance with workplace policies. However, this must be done transparently and with employee consent.
Cybersecurity professionals often test the security of Instagram accounts to identify vulnerabilities and improve online safety. Ethical hackers work within legal boundaries to strengthen cybersecurity and protect users from malicious attacks.
Some individuals may want to check a partner’s Instagram activity due to suspicions of infidelity or dishonesty. However, accessing someone’s Instagram account without permission violates privacy laws and ethical standards.
Is Hacking Instagram Account Ethical?
The ethics of hacking an Instagram account largely depend on intent, method, and legal considerations. While hacking is generally associated with illegal activities, certain scenarios may justify ethical monitoring or security testing. Below, we examine both perspectives.

1. The Unethical Side of Hacking Instagram
Hacking someone’s Instagram account without permission is considered unethical and illegal in most jurisdictions. The following actions fall under unethical hacking:
- Privacy Violation – Accessing someone’s Instagram account without consent is a breach of privacy and can lead to legal consequences.
- Identity Theft & Fraud – Hackers may steal login credentials for impersonation, financial fraud, or blackmail, which is both unethical and criminal.
- Misinformation & Harm – Unauthorized access can lead to account misuse, such as spreading false information or damaging reputations.
2. Ethical Situations for Instagram Monitoring
Certain circumstances may justify ethical monitoring or security testing of an Instagram account:
- Parental Monitoring for Child Safety – Parents may use monitoring tools to protect their children from cyberbullying, inappropriate content, or online predators. However, transparency and consent (depending on the child’s age) are essential.
- Recovering a Hacked or Lost Account – If someone loses access to their Instagram account due to hacking or forgotten credentials, ethical hacking techniques (such as password recovery or security audits) can help regain control.
- Cybersecurity & Ethical Hacking – Security professionals may ethically test Instagram’s security by identifying vulnerabilities to improve digital safety. This form of hacking follows strict legal and ethical guidelines.
- Employee Monitoring on Company Devices – Employers may monitor social media activity on company-owned devices to ensure workplace compliance, but only with employee consent and clear policies in place.
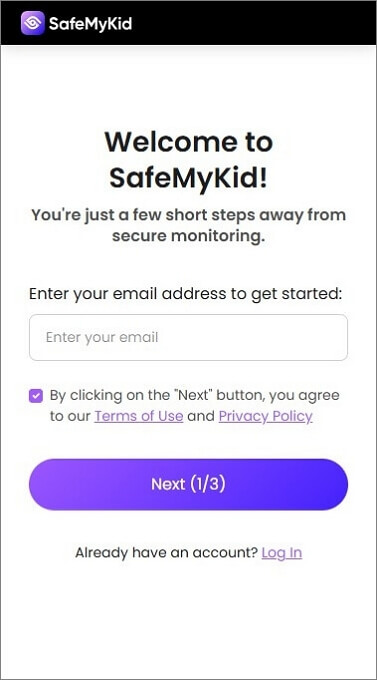
SafeMyKid: The Best Way to Monitor Instagram Effortlessly
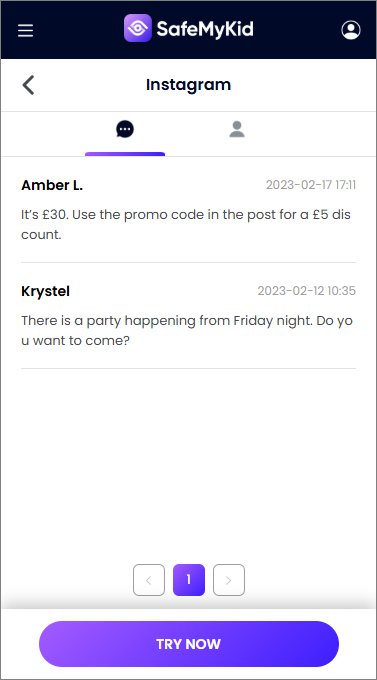
SafeMyKid is a comprehensive and reliable parental control tool that allows guardians to monitor their children's Instagram activities without resorting to unethical or illegal hacking methods.
This powerful software provides a safe, legal, and efficient way to ensure online safety by tracking messages, posts, and interactions in real-time.
Unlike hacking techniques that violate privacy and security, SafeMyKid operates transparently, giving parents the ability to responsibly oversee their child’s digital behavior while promoting a secure online experience.

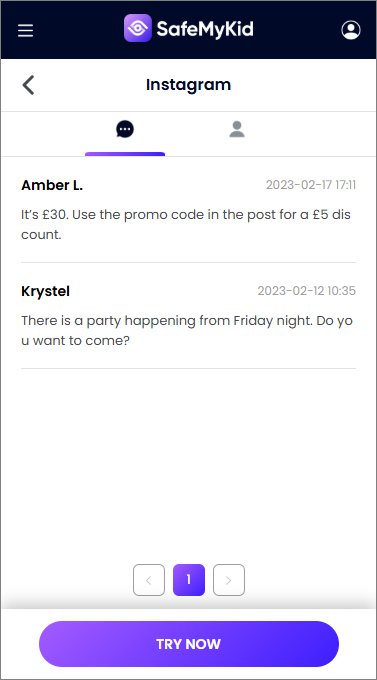
Key Features of SafeMyKid Instagram Account Hacker
SafeMyKid provides a powerful solution for monitoring Instagram accounts, ensuring online safety, and preventing unauthorized access. Designed with security and parental control in mind, SafeMyKid offers a range of advanced features to help users track activity responsibly.
- Monitor Instagram Messages, Posts, and Interactions: Track direct messages, comments, and post engagements in real time.
- View Browsing History and Screen Time: Gain insights into the user's Instagram activity, including time spent on the platform and visited profiles.
- Stealth Mode Monitoring: Operates discreetly in the background without alerting the Instagram account owner.
- App Usage and Activity Reports: Get detailed logs of Instagram usage patterns, including most active hours and frequent interactions.
How to Use SafeMyKid Instagram Account Hacker
Whether you're using an Android or iPhone device, SafeMyKid setup is quick and hassle-free, allowing you to start monitoring within minutes. Follow these step-by-step instructions to get started.
How to Hack Instagram Account on Android Devices
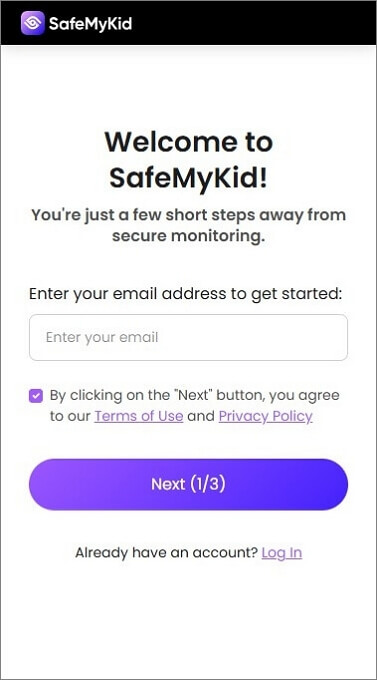
Step 1. Sign Up
Create an account on the SafeMyKid platform.
Step 2. Set Up the SafeMyKid to Hack Instagram Account
Install SafeMyKid on the target Android device. Follow the provided on-screen instructions to configure monitoring preferences, and enable necessary permissions.
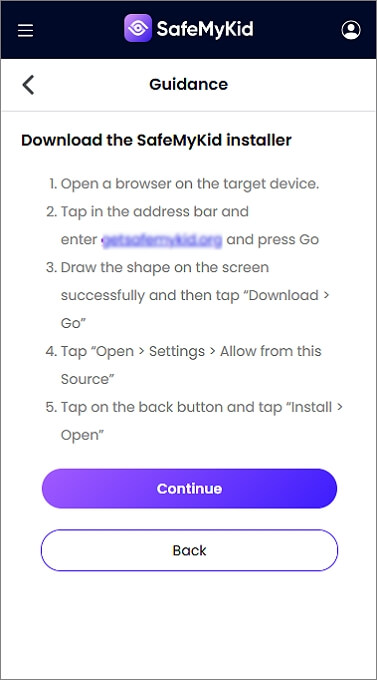
Step 3. Hack Instagram Account on Android
Access the SafeMyKid dashboard from your device to track Instagram messages, posts, and interactions in real time.
How to Hack Instagram Account on Apple Devices
Step 1. Sign Up
Register for a SafeMyKid account.
Step 2. Sync iCloud Account
Enter the iCloud credentials of the target device to enable tracking. No need to install an app.
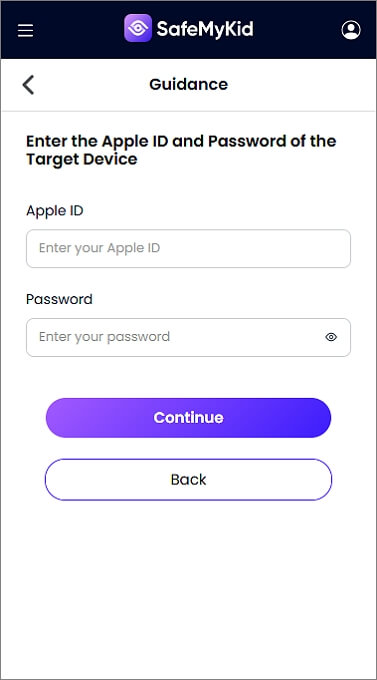
Step 3. Hack Instagram Account on iPhone
Use the SafeMyKid dashboard to view Instagram activity, including messages, posts, and login attempts.
Reasons to Recommend SafeMyKid Instagram Hacker
SafeMyKid stands out as a reliable solution for monitoring Instagram activity. Whether you're a concerned parent, guardian, or employer, this tool offers a secure way to track online interactions without violating privacy laws. Here are the key reasons why SafeMyKid is highly recommended:
- Legal and Ethical Monitoring: SafeMyKid ensures compliance with ethical monitoring standards, allowing parents and guardians to track their child's activity responsibly.
- Easy Setup with a User-Friendly Interface: The platform is designed for hassle-free installation and intuitive navigation, making it accessible even for users with minimal technical experience.
- Ideal for Parental Control and Online Safety: Parents can monitor messages, posts, and interactions to protect children from cyberbullying, online predators, and inappropriate content.
- Remote Access and Real-Time Updates: Users can track Instagram activity from any device via a secure online dashboard, ensuring instant updates and alerts.
5 Other Effective Ways on How to Hack Instagram Account
Hacking an Instagram account requires understanding various techniques used by cybersecurity professionals and hackers. Here are five effective ways to hack an Instagram account.
1. Phishing Attacks: A Common Instagram Hacking Method

Phishing is a deceptive hacking technique that manipulates users into unknowingly disclosing their Instagram login credentials. This is done by redirecting them to a fraudulent login page designed to mimic the official Instagram website.
Once the victim enters their username and password, the hacker captures the information and gains unauthorized access to the account. Phishing attacks are often carried out through emails, text messages, or social media links, making them a common yet dangerous method of hacking.
Users who do not carefully check website URLs or security indicators are particularly vulnerable to this type of attack.
How Does It Work?
- The hacker creates a fake Instagram login page.
- A link to this page is sent via email, direct messages, or other channels.
- The victim enters their username and password, thinking it’s the official site.
- The hacker captures the credentials and gains unauthorized access.
Limitations:
- Requires good social engineering skills.
- Two-factor authentication (2FA) can prevent unauthorized logins.
- Users who check URLs carefully won’t fall for this trick.
2. Keylogging: Monitoring Every Keystroke
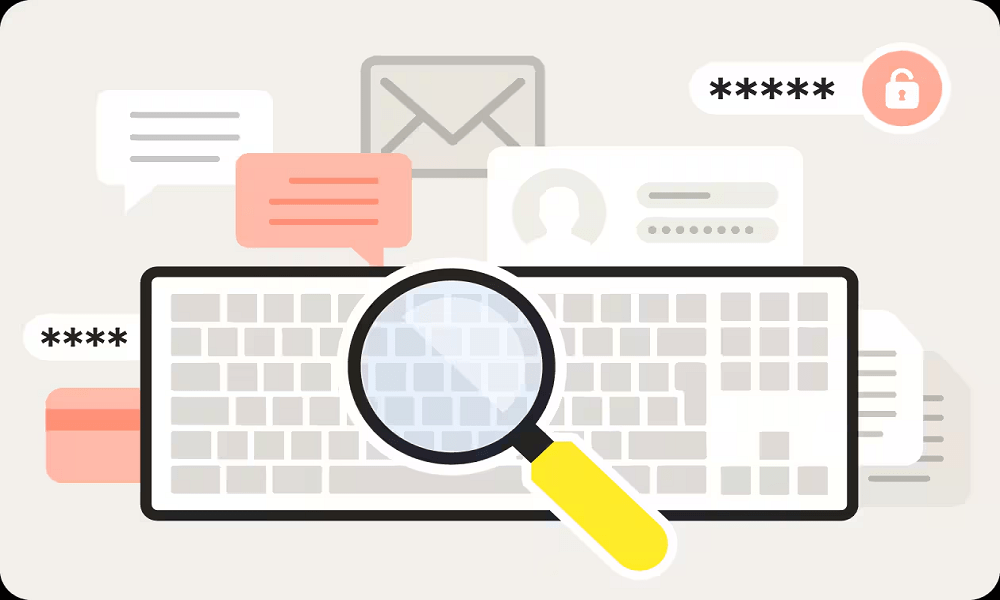
Keylogging is a hacking technique that involves the use of specialized software or hardware to track and record every keystroke made on a target’s device.
Hackers use keyloggers to capture sensitive information, including Instagram usernames and passwords, without the victim’s knowledge. These malicious programs often run in the background, making them difficult to detect.
Keyloggers can be installed through phishing emails, malicious downloads, or even physical access to a device. Once installed, they continuously log everything typed, allowing hackers to steal login credentials and gain unauthorized access to Instagram and other personal accounts.
How Does It Work?
- The hacker installs a keylogger on the victim’s phone or computer.
- The keylogger records every keystroke, including passwords.
- The hacker retrieves the recorded data and logs into Instagram.
Limitations:
- Requires physical access to install the keylogger.
- Antivirus programs can detect and remove keylogging software.
- Some advanced keyloggers require technical expertise.
3. Social Engineering: Exploiting Human Psychology
Social engineering is a psychological manipulation technique used by hackers to deceive individuals into willingly revealing sensitive information, such as Instagram login credentials. This method relies on exploiting human trust rather than technical vulnerabilities.
Hackers may impersonate a trusted friend, a customer support agent, or an official Instagram representative to persuade victims into sharing their passwords or clicking on malicious links.
Social engineering attacks can occur through emails, phone calls, or direct messages, often creating a sense of urgency to pressure the target into acting without suspicion. This makes it a highly effective and dangerous hacking method.
How Does It Work?
- The hacker impersonates Instagram support or a friend.
- They contact the target with a believable excuse (e.g., "Your account has been compromised").
- The victim voluntarily provides login credentials, thinking it’s a legitimate request.
Limitations:
- Requires the hacker to be highly persuasive.
- Not effective on tech-savvy users.
- Users with 2FA enabled have extra protection.
4. Password Cracking Tools: Breaking Weak Passwords

Password cracking tools are specialized software programs designed to break into accounts by systematically guessing passwords through brute-force attacks.
These tools use automated trial-and-error processes to test thousands or even millions of possible password combinations in a short period. Weak or commonly used passwords, such as “123456” or “password,” are especially vulnerable to this method.
Some advanced cracking tools also use dictionary attacks, where they try precompiled lists of common passwords to speed up the process. If an Instagram account has a weak or reused password, it becomes an easy target for hackers using these sophisticated cracking techniques.
How Does It Work?
- The hacker runs an automated tool that tests thousands of password combinations.
- If the password is weak (e.g., "123456" or "password"), it can be cracked in seconds.
- The hacker logs into Instagram once they find the correct password.
Limitations of Password Cracking Tools:
- Very slow for strong passwords.
- Illegal and violates Instagram’s terms of service.
- Some tools require advanced technical knowledge.
5. Session Hijacking: Taking Over Active Sessions
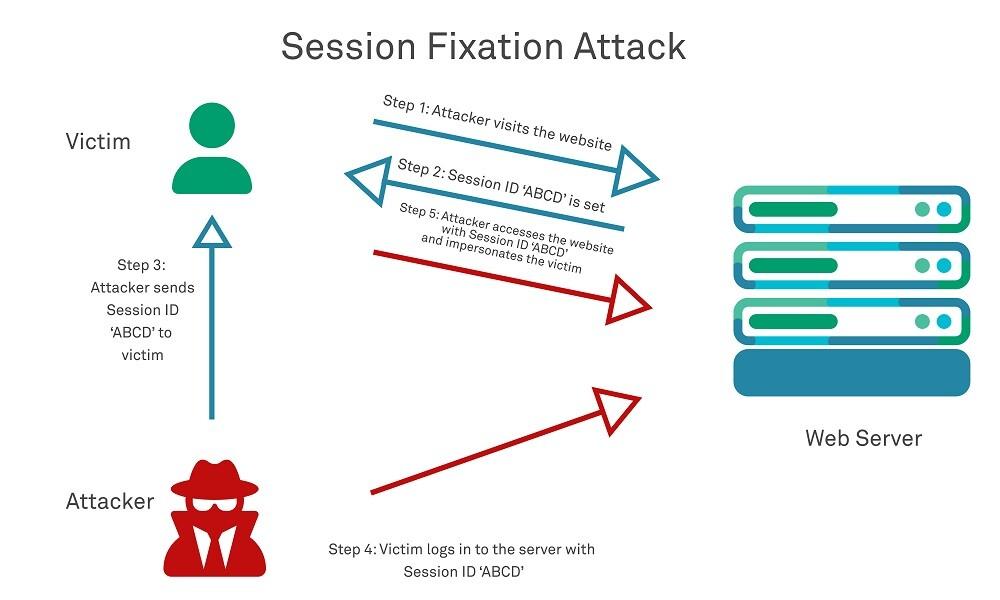
Session hijacking is a hacking technique where cybercriminals intercept network traffic to steal session cookies, allowing them to gain unauthorized access to an active Instagram session without needing the actual login credentials.
Session cookies are small pieces of data stored on a user's device that authenticate their session with Instagram. Hackers often exploit unsecured Wi-Fi networks or use malware to capture these cookies, enabling them to take control of an account without the victim realizing it.
Since session hijacking bypasses the login process, it can be challenging to detect and can lead to significant privacy and security breaches.
How Does It Work?
- The hacker uses packet sniffing tools on public Wi-Fi networks.
- They capture the session cookies, which store login credentials.
- The hacker uses these cookies to gain access without needing a password.
Limitations:
- Requires advanced networking knowledge.
- Only works on unsecured networks.
- VPNs and HTTPS encryption help prevent session hijacking.
Comparing Instagram Hacking Methods: Which One is Safe and Effective?
When it comes to monitoring or gaining access to an Instagram account, various methods exist—some ethical, others outright illegal. Below is a comparison of popular techniques, highlighting their ease of use, stealth capabilities, and legal implications.
| Method | Ease of Use | Stealth | Legal & Ethical? | Effectiveness | Best For |
|---|---|---|---|---|---|
| SafeMyKid (Recommended) | ⭐⭐⭐⭐⭐ | High | 100% Legal | ⭐⭐⭐⭐⭐ | Parental monitoring, ethical tracking |
| Phishing Attacks | ⭐⭐⭐ | Low | Illegal | ⭐⭐ | Cybercriminals exploiting careless users |
| Keylogging | ⭐⭐⭐ | High | Illegal | ⭐⭐⭐ | Hackers with physical or malware access |
| Social Engineering | ⭐⭐ | Low | Unethical | ⭐⭐⭐ | Skilled manipulators exploiting trust |
| Password Cracking Tools | ⭐ | Low | Illegal | ⭐⭐ | Cracking weak passwords |
| Session Hijacking | ⭐⭐ | High | Illegal | ⭐⭐⭐ | Advanced hackers targeting unsecured Wi-Fi |
SafeMyKid is the only legal and ethical solution designed for responsible monitoring, while all other methods involve privacy violations and potential legal consequences.
Limitations of Third-Party Monitoring Apps:
While third-party monitoring apps offer various tracking features, many come with significant drawbacks that can compromise security, privacy, and functionality. Here are some common limitations:
- Lack of Reliability: Many monitoring apps claim to provide real-time tracking, but in reality, they often suffer from technical glitches, delayed updates, or even complete failure to retrieve data.
- Device Compatibility Issues: Some monitoring apps may not work properly across different operating systems, leading to inconsistent performance on Android and iOS devices.
- Requirement for Jailbreaking or Rooting: Many apps require users to jailbreak (iPhone) or root (Android) their devices, which not only voids warranties but also exposes devices to security risks and malware.
- Privacy and Data Security Concerns: Unreliable third-party apps may store or misuse sensitive information, making users vulnerable to data breaches or unauthorized access.
- Hidden or Ongoing Costs: Some apps advertise free features but later require costly subscriptions or hidden charges to unlock full functionality.
- Limited Customer Support: Many third-party apps offer little to no customer support, leaving users stranded when technical issues arise.
Unlike many unreliable third-party apps, SafeMyKid offers a secure, ethical, and user-friendly monitoring solution. With SafeMyKid, you get a trusted and legally compliant monitoring tool that ensures both security and peace of mind.
FAQs on How to Hack Instagram Account
When it comes to monitoring Instagram accounts, many people have questions about legality, ethics, and the best tools available. Below are some frequently asked questions to help clarify important aspects of Instagram monitoring.
1. Is it legal to monitor someone’s Instagram activity?
Monitoring someone’s Instagram activity is legal only if you have their consent or if you are a parent supervising a minor. Unauthorized access to someone’s account without permission is illegal and violates privacy laws.
2. Can Instagram detect and block hacking attempts?
Yes, Instagram has advanced security measures, such as login alerts, two-factor authentication, and AI-driven fraud detection, to identify and prevent hacking attempts. If suspicious activity is detected, Instagram may temporarily lock or suspend an account.
3. How can I protect my Instagram account from hackers?
To secure your account, use a strong, unique password, enable two-factor authentication (2FA), avoid clicking on suspicious links, and regularly monitor login activity. Also, be cautious when using public Wi-Fi networks.
4. Does SafeMyKid require physical access to the target device?
Yes, SafeMyKid requires one-time physical access to install the app on an Android device. However, for iPhones, it works without installation by syncing with iCloud credentials.
5. What should I do if my Instagram account gets hacked?
If your account is hacked, immediately reset your password, enable two-factor authentication, and check for any unauthorized changes in account settings. You can also report the incident to Instagram for recovery assistance.
Conclusion
While there are several ways on how to hack an Instagram account, most of them involve unethical or illegal methods. For those looking for a safe and reliable way to monitor Instagram activity—especially parents—SafeMyKid is the best solution.
It offers a legitimate and effortless way to track Instagram interactions without violating privacy laws. Always use ethical monitoring methods and prioritize security when accessing any social media account.