The Definitive Guide To Instagram Password Hacks: 7 Powerful Techniques You Must Try

Instagram password hacks are a widely discussed yet highly controversial topic, often involving methods that are illegal, unethical, and a violation of privacy.

Hacking into someone’s Instagram account without their explicit permission is not only a breach of trust but also a criminal offense. Such actions can result in severe legal consequences, including fines, lawsuits, and even imprisonment.
Why Instagram Password Hacks Are a Growing Concern
With millions of active users, Instagram is a prime target for hackers looking to steal personal information, spread scams, or take control of high-profile accounts. Cybercriminals use various hacking methods, from phishing to brute force attacks, to break into accounts.
Understanding these hacking techniques is the first step in protecting your account from unauthorized access. Let’s dive into the details.
How to Tell If Your Instagram Password Has Been Hacked
Detecting an Instagram password hack early can help protect your account from further harm. Be alert for warning signs of unauthorized access, such as unexpected login attempts, password changes, or unfamiliar activity.
Identifying these red flags early can help you secure your account before more damage occurs.
- Login Attempts from Unknown Locations – Receiving alerts about logins from unfamiliar places.
- Unrecognized Activity – Posts, messages, or follows you didn’t authorize.
- Changed Account Details – Your email, phone number, or password has been altered without your knowledge.
- Inability to Log In – Your password no longer works, despite entering it correctly.
- Unusual DMs Sent from Your Account – Friends report receiving suspicious messages from you.
- Security Alerts from Instagram – Emails notifying you of password or setting changes.
7 Common Techniques for an Instagram Password Hack

Hackers use various techniques to gain unauthorized access to Instagram accounts. Understanding these methods can help you take proactive security measures. Here are seven common password-hacking techniques, along with their pros and cons.
1. Phishing Attacks
Phishing deceives users into revealing their login details through fake websites, emails, or messages. These scams mimic Instagram’s official communication to appear legitimate. Users unknowingly enter credentials, giving hackers access to their accounts.
Pros:
- Easy to execute with minimal technical skills.
- Can target multiple users simultaneously.
- Works on users unaware of security threats.
- No need for direct access to the victim’s device.
Cons:
- Requires user interaction to succeed
- Many users are now aware of phishing scams
- Security features like email warnings can prevent phishing attempts
2. Brute Force Attacks
This method uses automated tools to repeatedly try different password combinations until the correct one is found. It relies on trial and error, making it effective against weak passwords. Strong security measures can help prevent such attacks.
Pros:
- Can crack weak passwords effectively.
- Works without needing social engineering.
- Automated tools make it easier.
- Doesn’t rely on user interaction.
Cons:
- Time-consuming to strong passwords.
- Instagram limits failed login attempts.
- Strong encryption can render this method useless.
3. Social Engineering
Hackers trick victims into sharing their passwords by posing as trusted sources, such as Instagram support or a friend. This psychological manipulation exploits trust rather than technical vulnerabilities. Awareness and verification can help prevent such attacks.
Pros:
- Doesn’t require technical hacking skills
- Can bypass even strong passwords if the victim falls for the trick
- Works through multiple channels like calls, messages, or fake profiles
- Harder to detect by automated security systems
Cons:
- Requires the victim to fall for deception
- Training and awareness can make this method ineffective
- Time-consuming compared to automated attacks
4. Exploiting Weak Passwords
Hackers take advantage of weak passwords like "123456" or "password" by testing commonly used credentials. They frequently use leaked databases to identify matches quickly.
Creating strong, unique passwords reduces the risk of such attacks and helps protect your account from unauthorized access.
Pros:
- Quick and effective against weak passwords
- No need for advanced hacking tools
- Can be automated for large-scale attacks
- Works well with publicly available password lists
Cons:
- Useless against strong, unique passwords
- Instagram enforces password strength requirements
- Security alerts can notify users of unauthorized login attempts
5. Rainbow Table Attacks
This method uses precomputed hash values to speed up password cracking by matching them with stored encrypted passwords. It is effective against weak encryption but fails against strong hashing with salting. Robust security measures can help prevent such attacks.
Pros:
- Faster than brute force attacks
- Effective against weak encryption
- Works well on databases with unsalted hashes
- Can be automated for efficiency
Cons:
- Requires large storage for hash databases
- Ineffective against strong encryption with salting
- Not useful for real-time attacks
6. Spidering
Hackers analyze a target’s interests, behavior, and personal details to guess their password. This method is effective against users who rely on easily guessable information. Using complex, unique passwords can help prevent such attacks.
Pros:
- Helps hackers create highly accurate guesses
- Works well when users use predictable passwords
- Can be used alongside other techniques for better success
- Doesn’t require technical hacking tools
Cons:
- Time-intensive and requires detailed research
- Strong, unique passwords make it ineffective
- Awareness of this technique can help users avoid predictable passwords
7. Shoulder surfing
A social engineering technique known as "shoulder surfing" occurs when someone watches someone enter private data, including login credentials. Although it is frequently linked to ATM PIN theft, it is not limited to financial activities.
Pros:
- Easy access to sensitive information.
- Hard to detect in crowded areas.
- Bypasses digital security measures.
- Works in various public settings.
Cons:
- Leads to password and data theft.
- Difficult to notice in real time.
- Can result in identity theft or fraud.
How to Hack Instagram without Password by Third-Party App: Meet SafeMyKid

Some third-party apps, like SafeMyKid, are intended for parental control but can be exploited to access Instagram accounts without permission. Hackers misuse these apps to monitor or steal login details. Avoiding untrusted apps helps protect your account.
Instagram password hack is a growing concern, highlighting the need for secure and transparent digital communication. SafeMyKid provides a smart solution by monitoring app activity, tracking login attempts, and sending real-time alerts for suspicious behavior.
With its advanced security features, SafeMyKid helps prevent unauthorized access and ensures that online interactions remain safe and accountable. By using this tool, you can protect your digital presence, strengthen security, and foster trust across various platforms.
Key features of Safemykid for Instagram Hacking without Password
- Login Activity Monitoring – Tracks Instagram login attempts and detects unauthorized access.
- App & Web Restrictions – Blocks access to suspicious apps or websites that may compromise account security.
- Suspicious Login Alerts – Sends real-time notifications for unusual login attempts or password changes.
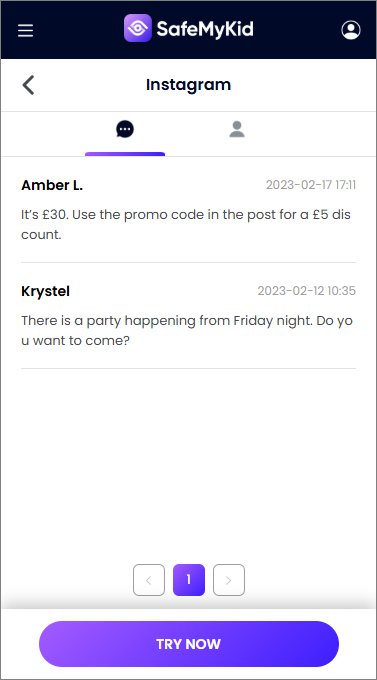
- Message & Call Oversight – Helps monitor conversations for any security threats or phishing attempts.
- Screen Time Management – Limits device usage to prevent excessive social media exposure.
- Real-Time Location Tracking – Uses GPS to track device activity for added security.
- Geofencing Notifications – Alerts users when a device enters or leaves a designated safe zone.
- Stealth Monitoring Mode – Operates discreetly to detect unauthorized Instagram access.
- Detailed Security Reports – Provides insights into Instagram login patterns and potential hacking attempts.
How to Hack an Instagram without Password Using SafeMyKid
SafeMyKid is designed to enhance security and prevent unauthorized access to Instagram accounts. Here’s how you can use it:
Step 1. Sign Up for an Account
Register on the SafeMyKid website using your email. After completing the signup process, you'll gain access to the app's dashboard.
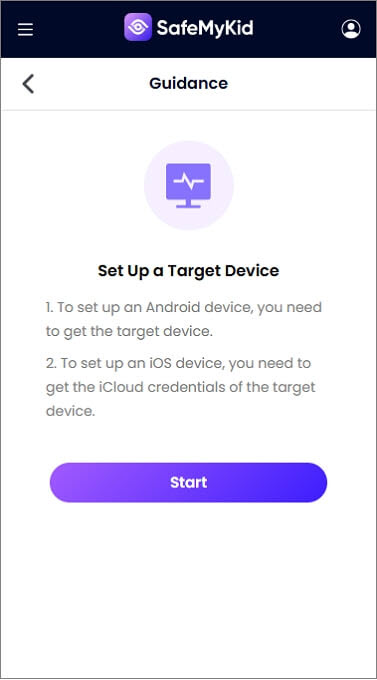
Step 2. Set Up the App
For iPhones – Log in using the iCloud credentials linked to the target device; no installation is needed.
For Android Devices – Download and install the app on the target device, where it operates discreetly in stealth mode.
Step 3. Hacking Instagram Activity via SafeMyKid Dashboard
With SafeMyKid, you can track login attempts, detect suspicious activity, and hack Instagram interactions, ensuring a secure and responsible online experience.
FAQs About Instagram Password Hack
If you're curious about Instagram password hacks, you likely have questions about how they work and their implications. Below, we’ve answered some of the most frequently asked questions to help you better understand this topic.
1. Are there ethical ways to hack an Instagram password?
Yes, ethical hacking involves authorized professionals testing Instagram's security systems to identify and fix vulnerabilities. This is done with permission and aims to improve overall account safety.
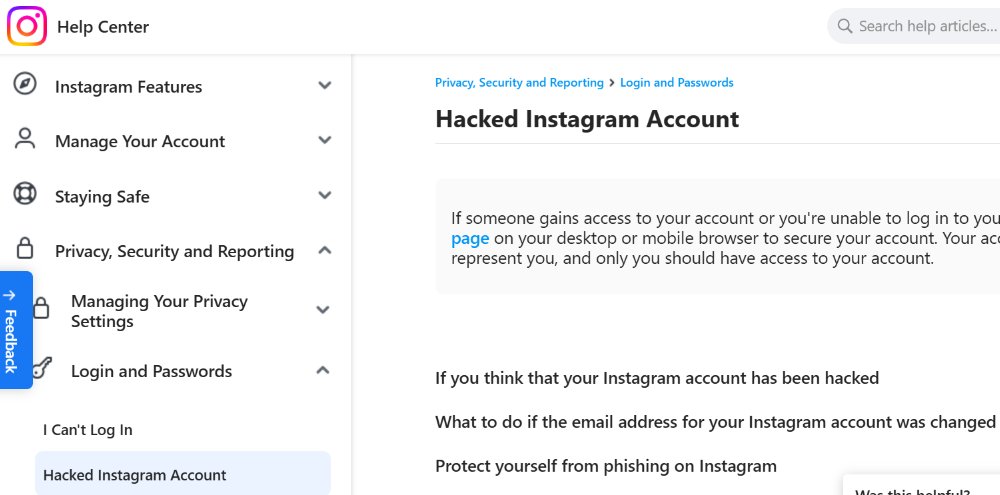
2. What should I do if my Instagram password is hacked?
Immediately reset your password, enable two-factor authentication, and check for unauthorized devices in your account settings.
3. Can hackers retrieve my Instagram password?
Hackers use techniques like phishing, brute force attacks, and leaked password databases to gain access, but strong passwords and security measures can prevent this.
4. How can I protect my Instagram from password hacks?
Use a strong, unique password, enable two-factor authentication, avoid suspicious links, and monitor your account activity regularly.
5. Is there a tool to monitor unauthorized Instagram access?
Yes, security tools like SafeMyKid can track login attempts, detect suspicious activity, and send real-time alerts to help prevent hacking attempts.
Conclusion
Instagram password hack threats are increasing, making strong security measures essential. Hackers use brute force and phishing attacks, but strong passwords can prevent them.
Regularly monitoring account activity and staying informed about hacking techniques can help prevent unauthorized access. Protecting your Instagram account requires vigilance and proactive security habits.




