Telegram Hack: 7 Ways Accounts Get Hacked & Fixes

If you’re wondering whether your account is safe, you need to understand how these Telegram hacks work and what you can do to prevent them.

This article will explore seven ways hackers target Telegram, how to recognize if your account has been hacked, and the best ways to monitor Telegram.
What is Telegram Hack?
Telegram hacking refers to unauthorized attempts to access a user's account, messages, or personal data. While Telegram is known for its strong security features, attackers use various techniques to exploit vulnerabilities and compromise accounts.

Common Telegram Hack Methods:
- Phishing Attacks: Fake login pages trick users into entering credentials.
- Session Hijacking: Hackers intercept session tokens to gain access.
- Spyware & Keyloggers: Malicious software that records keystrokes and activity.
- SIM Swap Attacks: Attackers transfer a victim’s phone number to a new SIM card.
- Social Engineering: Manipulating users into revealing sensitive information.
- Malicious Bots & Links: Harmful bots distribute malware or steal data.
- Weak Password Exploits: Easy-to-guess passwords make accounts vulnerable.
While these methods pose a risk, you can protect your Telegram account with strong passwords, two-step verification, and cautious online behavior. Read on to learn how hackers operate and how to keep your account secure.
Why is Telegram Hacking Necessary?

While hacking is often associated with malicious intent, there are certain scenarios where Telegram hacking may be considered necessary or justifiable. Below are some reasons why individuals or organizations might attempt to access a Telegram account:
- Parental Monitoring
- Recovering a Lost Account
- Investigative Purposes
- Employee Surveillance
- Checking for Security Vulnerabilities
Parents may need to track their children’s online activities to ensure their safety from cyberbullying, predators, and inappropriate content. Ethical monitoring tools can help parents supervise their kids' Telegram interactions.
If someone loses access to their Telegram account due to hacking, forgotten credentials, or SIM card issues, ethical hacking techniques might be used to regain access. This includes social engineering methods or security loopholes that allow recovery.
Law enforcement agencies or cybersecurity experts may hack Telegram accounts to track criminal activities, such as fraud, terrorism, or illegal trading. Ethical hacking methods are often employed to gather digital evidence.
Companies may need to monitor Telegram communications on work devices to prevent data leaks, corporate espionage, or insider threats. This is especially relevant for industries dealing with sensitive information.
Cybersecurity professionals conduct penetration testing on Telegram accounts to identify and patch security flaws. Ethical hackers analyzed Telegram’s security mechanisms to improve overall data protection.
Although there are legitimate reasons for hacking Telegram, unauthorized access to someone’s account without consent is illegal and unethical. It is always advisable to use ethical methods and legal tools for security and monitoring purposes.
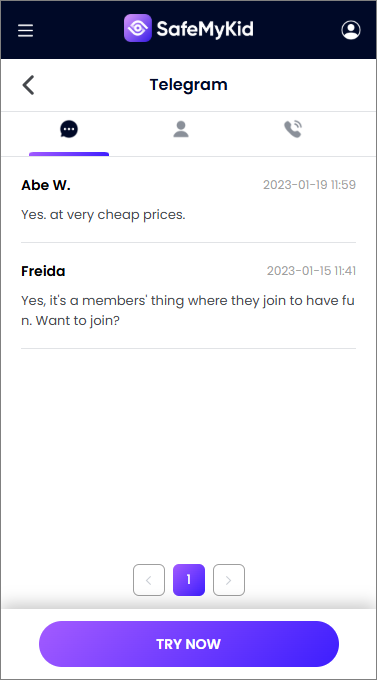
SafeMyKid: The Best Way to Monitor Telegram
If you want to monitor Telegram activity for safety reasons, SafeMyKid is the best solution available.

Unlike other tracking apps that may compromise user privacy, SafeMyKid ensures a secure, reliable, and discreet way to monitor Telegram messages without exposing data to third parties.
It provides real-time access to messages, tracks login activity, and helps users detect suspicious behavior, making it an ideal choice for secure monitoring.
Key Features of SafeMyKid Telegram Hacker
SafeMyKid offers advanced monitoring capabilities, making it an effective tool for tracking Telegram activity. Whether for parental control or security purposes, it provides users with deep insights into Telegram interactions. Key features of the SafeMyKid Telegram hacker include:
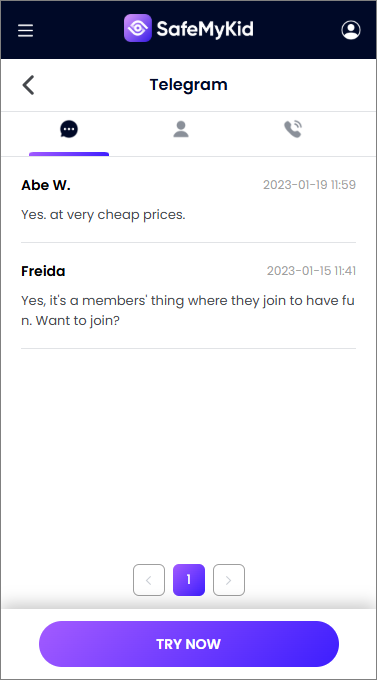
- View Telegram Messages in real time – Access sent and received messages instantly.
- Monitor Chat History – Detect deleted messages and suspicious conversations.
- Capture Screenshots – Remotely take screenshots of Telegram activity.
- Record Keystrokes – Log typed messages, even if they are unsent or deleted.
- Monitor Group Chats & Channels – Track activity in public and private Telegram groups.
- Detect Shared Media & Files – View images, videos, and documents exchanged on Telegram.
- Track Contact List & Call Logs – See saved contacts and any Telegram voice or video call history.
- Receive Alerts for Suspicious Activity – Get notified of unauthorized logins or account changes.
SafeMyKid provides discreet monitoring, ensuring users can track Telegram activity efficiently while maintaining security and privacy.
How to Set Up SafeMyKid Telegram Hacker
Setting up SafeMyKid for Telegram monitoring is a straightforward process, ensuring seamless tracking of messages, calls, and other activities. Follow these steps to begin monitoring Telegram on your target device.
How to Hack Telegram on Android Devices
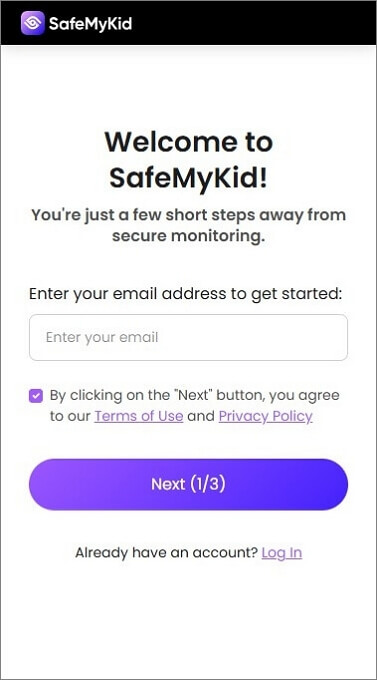
Step 1. Sign Up
Create an account on the SafeMyKid website.
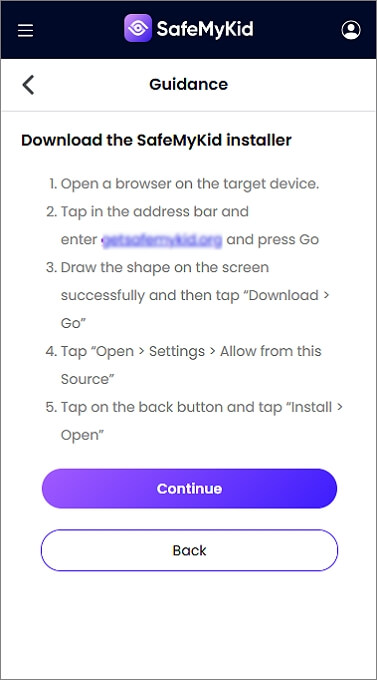
Step 2. Set Up SafeMyKid on Android
Install SafeMyKid on the target Android device. Follow the on-screen instructions to grant the necessary permissions.
Step 3. Hack Telegram on Android
Log in to your SafeMyKid account to view Telegram activity in real time.
How to Hack Telegram on Apple Devices
Step 1. Sign Up
Register on the SafeMyKid platform.
Step 2. Enter iCloud Credentials
Provide the target iPhone’s iCloud details to sync Telegram data.
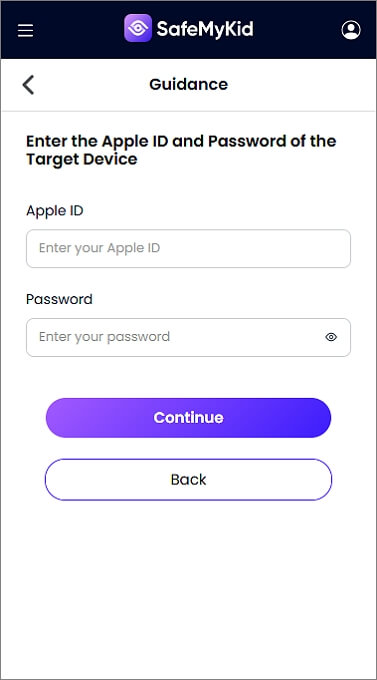
Step 3. Hack Telegram on iPhone
Use the SafeMyKid dashboard to view Telegram messages and shared media without installing software.
Why Choose SafeMyKid Telegram Hacker?
Unlike other monitoring tools that may pose security risks, SafeMyKid offers real-time tracking, an easy setup process, and a highly secure monitoring system.
It provides parental control features without violating security policies, ensuring that users can safely track Telegram activity without compromising data privacy.
With its advanced security measures, SafeMyKid is a reliable and effective solution for monitoring online activity.
7 Other Telegram Hack Methods
Hackers use various techniques to compromise Telegram accounts. Understanding these methods can help you stay protected. Let’s take a look at some of them
1. Session Hijacking: Exploiting Active Logins
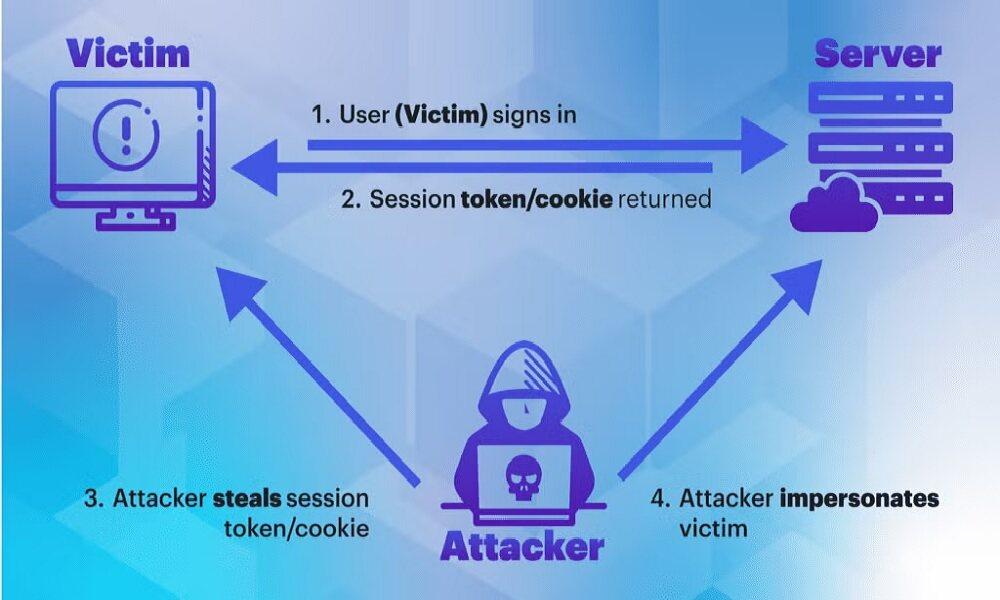
Telegram allows users to stay logged in across multiple devices, and hackers can exploit this feature. If a hacker gains access to session data through phishing or malware, they can control your account without needing your password.
Signs of a Hijacked Session
- Unrecognized devices listed under “Active Sessions”
- Messages sent that you didn’t write
- Random logouts from your account
How to Prevent This
- Regularly check “Active Sessions” in the Telegram settings
- Log out of unused devices
- Avoid clicking suspicious links that may contain malware
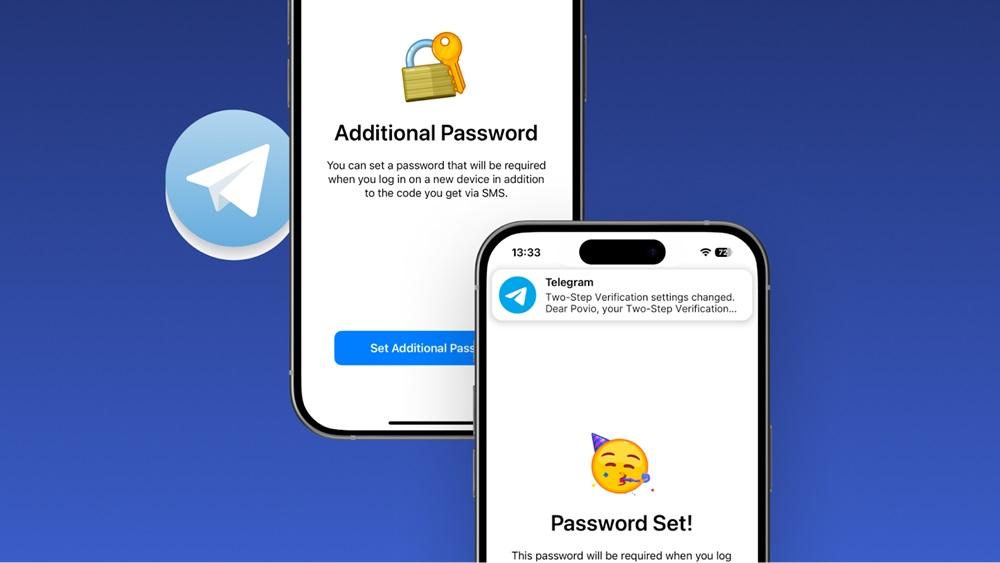
2. SIM Swapping: Bypassing Two-Factor Authentication

Hackers exploit SIM swapping by convincing mobile carriers to transfer your phone number to their SIM card. With control over your number, they intercept Telegram’s login codes, bypass two-factor authentication, and gain unauthorized access to your account.
Disadvantages of SIM-Based Authentication:
- This can be bypassed through social engineering
- Puts accounts at risk if the carrier is compromised
How to Prevent This
- Enable two-step verification in Telegram
- Contact your mobile provider to set up a SIM swap lock
- Use email-based authentication instead of SMS
3. Malware Attacks: Spying on Your Telegram Activity

Malware, disguised in apps or files, can secretly install itself on your device. Once active, it records keystrokes, captures screenshots, and steals Telegram session data, allowing hackers to monitor your messages and activity without your knowledge.
Limitations of This Method:
- Requires access to the victim’s device
- Antivirus software can sometimes detect and remove malware
How to Protect Yourself
- Avoid downloading apps from unknown sources
- Install a trusted antivirus program
- Regularly check your device for unusual activity
4. Phishing Attacks: Fake Telegram Logins
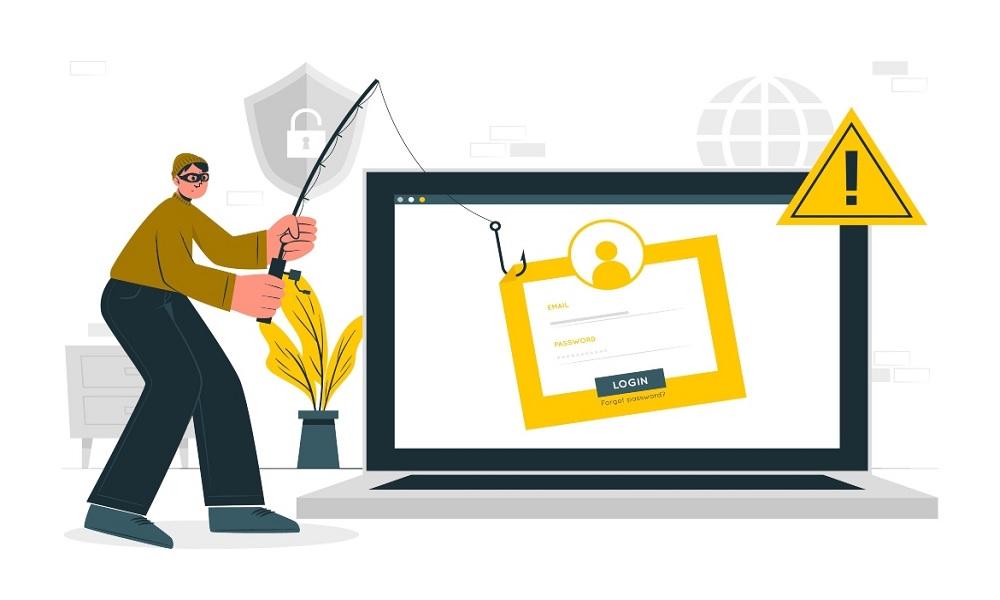
Hackers design fake Telegram login pages that closely resemble the official site. When users enter their credentials, the information is stolen, granting unauthorized access to their accounts. These scams are often spread through deceptive links in emails or messages.
Common Phishing Signs
- Emails or messages urging you to log in urgently
- Telegram support accounts asking for credentials
- Slightly altered website URLs
How to Stay Safe
- Always verify the URL before logging in
- Never share login codes with anyone
- Use a password manager to detect fake login pages
5. Third-Party Apps & Bots: Unintended Security Risks

Using unofficial Telegram apps or bots can expose your account to security risks. Some apps request unnecessary permissions or store login details improperly, making them vulnerable to hacking attempts and unauthorized access.
Examples of Risky Apps
- Unofficial Telegram clients with extra features
- Telegram bots that request sensitive account information
How to Avoid This
- Use only the official Telegram app
- Disable third-party bot permissions in the settings
6. Social Engineering: Manipulating Users
Hackers pretend to be Telegram support or a trusted contact, convincing users to share login codes or personal information. This method relies on deception rather than technical exploits, making it a common and effective hacking tactic.
How Hackers Trick Users
- Fake messages from “Telegram Support” asking for login codes
- Threats claiming your account will be deleted unless you verify your identity
How to Defend Against Social Engineering
- Telegram support never asks for login codes
- Enable two-step verification
- Verify identities before sharing sensitive information
7. Cloud Data Exploits: Telegram’s Storage Risks
Hackers who gain access to a Telegram account can retrieve chat history, media, and contacts stored in the cloud. Unlike secret chats, which use end-to-end encryption, regular chats rely on Telegram’s cloud storage, making them more vulnerable if an account is breached.
Disadvantages of Cloud Storage:
- Messages are retrievable even if deleted
- Chats can be accessed from any logged-in device
How to Secure Your Chats
- Use Secret Chats for sensitive conversations
- Regularly clear old messages
- Enable auto-delete for messages in important chats
How to Know If Your Telegram Has Been Hacked

If your Telegram account has been hacked, there are several warning signs to watch for. Hackers may gain unauthorized access and misuse your account without your knowledge. Here’s how to detect a possible breach:
- Unknown Devices Logged In – Check your active sessions by going to Settings > Devices in Telegram. If you see unfamiliar devices, your account may be compromised.
- Messages You Didn’t Send – If you notice messages in your chat history that you don’t remember sending, someone else might be using your account.
- Login Alerts from Telegram – Telegram sends login notifications when a new device accesses your account. If you receive an alert without logging in, it could indicate unauthorized access.
- Contacts Reporting Suspicious Activity – Friends may inform you about strange messages or requests from your account that you never sent.
- Settings or Profile Changes – If your profile picture, username, or privacy settings change without your input, it’s a strong sign of hacking.
- Unable to Access Your Account – If you’re suddenly logged out and can’t log back in, someone may have changed your credentials.
If you notice any of these signs, act immediately to secure your Telegram account.
What to Do If Your Telegram Account Is Hacked
If your Telegram account has been compromised, take immediate action to regain control and prevent further damage. Follow these steps:
- Log Out of All Active Sessions
- Open Telegram and go to Settings > Devices.
- Review the list of logged-in devices and terminate any suspicious sessions.
- This will log out the hacker and prevent further unauthorized access.
- Enable Two-Step Verification
- Go to Settings > Privacy & Security > Two-Step Verification and set up a password.
- This adds an extra layer of security by requiring a password in addition to the login code.
- Reset Your Password & Secure Your Email
- If your Telegram password has been compromised, change it immediately.
- Secure your linked email account by updating its password and enabling two-factor authentication (2FA).
- Check for Unauthorized Changes
- Review your profile, bio, and privacy settings to ensure nothing has been altered.
- Restore any unauthorized changes to prevent hackers from misleading your contacts.
- Warn Your Contacts
- Inform friends and family that your account was hacked to prevent them from falling for scams or phishing attempts sent from your profile.
- Contact Telegram Support (If Needed)
- If you're locked out of your account or the hacker has changed your phone number, visit Telegram Support for assistance.
- Provide details about your issue to regain access.
- Stay Vigilant & Monitor Your Account
- Regularly check for suspicious activity and update your security settings as needed.
- Avoid clicking on unknown links or downloading untrusted apps that may contain malware.
By acting quickly, you can minimize the damage and prevent future hacking attempts.
Frequently Asked Questions for Telegram Hack
Understanding how Telegram hacking works can help you protect your account from unauthorized access. Below are some common questions and answers.
1. Can someone hack my Telegram account without knowing my password?
Yes, hackers can access your Telegram account without knowing your password through session hijacking, phishing attacks, SIM swapping, and malware. These methods allow them to intercept login sessions, steal authentication codes, or control your device remotely.
2. How can I recover my Telegram account if it has been hacked?
If your Telegram account has been hacked, follow these steps immediately:
- Log out all active sessions from Telegram settings (if you still have access).
- Reset your password and enable two-step verification.
- Contact Telegram Support if you’re locked out and cannot recover access.
- Check for malware on your device, as it could be how the hacker gained access.
- Inform your contacts to be cautious of suspicious messages from your hacked account.
3. Is it possible to use Telegram without linking a phone number?
Telegram requires a phone number for initial registration, but you can use virtual numbers or secondary SIM cards for added privacy. However, keep in mind that using a disposable number may make account recovery difficult if you lose access.
4. Can hackers read my secret chats on Telegram?
No, Secret Chats in Telegram are end-to-end encrypted, meaning that messages are stored only on the sender’s and receiver’s devices. Even Telegram itself cannot access or decrypt them.
- Are third-party Telegram bots safe to use?
Not all third-party Telegram bots are safe. Some require unnecessary permissions that could expose your data to external threats. Bots that request access to your contacts, messages, or login details should be avoided.
6. Can I track someone’s Telegram activity legally?
Tracking someone’s Telegram activity without their consent is illegal in most countries, except when done for parental control or employee monitoring with proper authorization. SafeMyKid provides a legal way for parents to monitor Telegram activity.
Conclusion
Telegram hacks are carried out using multiple methods to target accounts. However, if you need to monitor Telegram activity for safety reasons, SafeMyKid provides a reliable solution.
By taking proactive measures, you can keep your Telegram chats safe and prevent unauthorized access. Stay vigilant, and don’t let hackers gain control of your account!
